Poem
Day and night
Night and day
No one asks why we turn this way
- Tags
- Lexical
Hitler gets the mobile bill
- Tags
- Films
FSM

- Tags
- Lexical
Twelvety
In an effort to develop software while travelling, without having to lug a laptop or use a fiddly on-screen keyboard, I've put together a small keyboard.
 Read more
Read more
First for animal welfare?
Maybe not first? You put the cow in a pie, in a box. Do you see?
- Tags
- Tips
Ryanair
Ryanair is the same backwards, in an Irish accent.

- Tags
- Lexical
Game Over
I finally finished a game. I don't mean I played a game and completed it, I rarely do that, I get so carried away looking at the scenery and lighting. No - I finished writing a game.
Read moreMr. Cola killed my pop
I like pop. I used to drink it every lunchtime. The worst place to buy pop is from a place with a "Coke fridge". My heart sinks when I see one. Everything in there will be from a small, prescribed selection of boring, globalised, bland drinks. The best place to buy pop is from a place with a "free-house" fridge. They're usually a bit shabbier, and are becoming rarer, but promise variety and taste. There could be anything in there: drinks you may not have heard of, as well as flavoursome ones like Irn Bru and Vimto.
For a while I used to go to a Marks and Spencer's (M&S) for lunch and so bought their pop. They have a great selection: ginger beer, cranberry lemonade, orange, cloudy lemonade and cola. Each of these comes in a diet variety which doesn't taste like battery acid like other diet drinks. I'd rotate through the flavours but preferred the cola: it actually had a cola flavour - unlike Coca-Cola which paled in comparison.
Then, around 2016, I'm not sure exactly when, their cola disappeared. Gone. Vanished. The other flavours were still there, but no cola. Weird.

I did notice at the same time that Coke appeared in its place. Marks and Spencer never sold Coke before then. Why would they when they had a better version? If their orange had been replaced by Tango or their ginger beer by Idris for example, that wouldn't have been so bad. But their cola and Coke were polar opposites in flavour: it was the worst one to replace. Obviously I didn't buy the insipid usurper and so cola was gone, but not forgotten, from my lunch rotation.

I thought it might be temporary, or just in my region, but no. The good cola had been replaced throughout the UK (or Europe for all I know). Wow. That was some shelf-prioritisation marketing pressure, I thought, but maybe I can still get the good cola from the back of the shop. I asked the staff but no one was aware of the swap. I looked online expecting some kind of campaign on behalf of people up-in-arms about losing their tasty cola, but nothing. And still in 2020 there is no mention of it online. I can barely find a picture of the old M&S cola, let alone an article about its loss.
If I search the M&S website I get:
"We found 0 results for cola, but here's what we found for cool".
So I keep digging over the years, because I really miss the cola flavour and wonder why no one else does, and still nothing. Until today - I find a clue; I make a possible link; an explanation, perhaps.
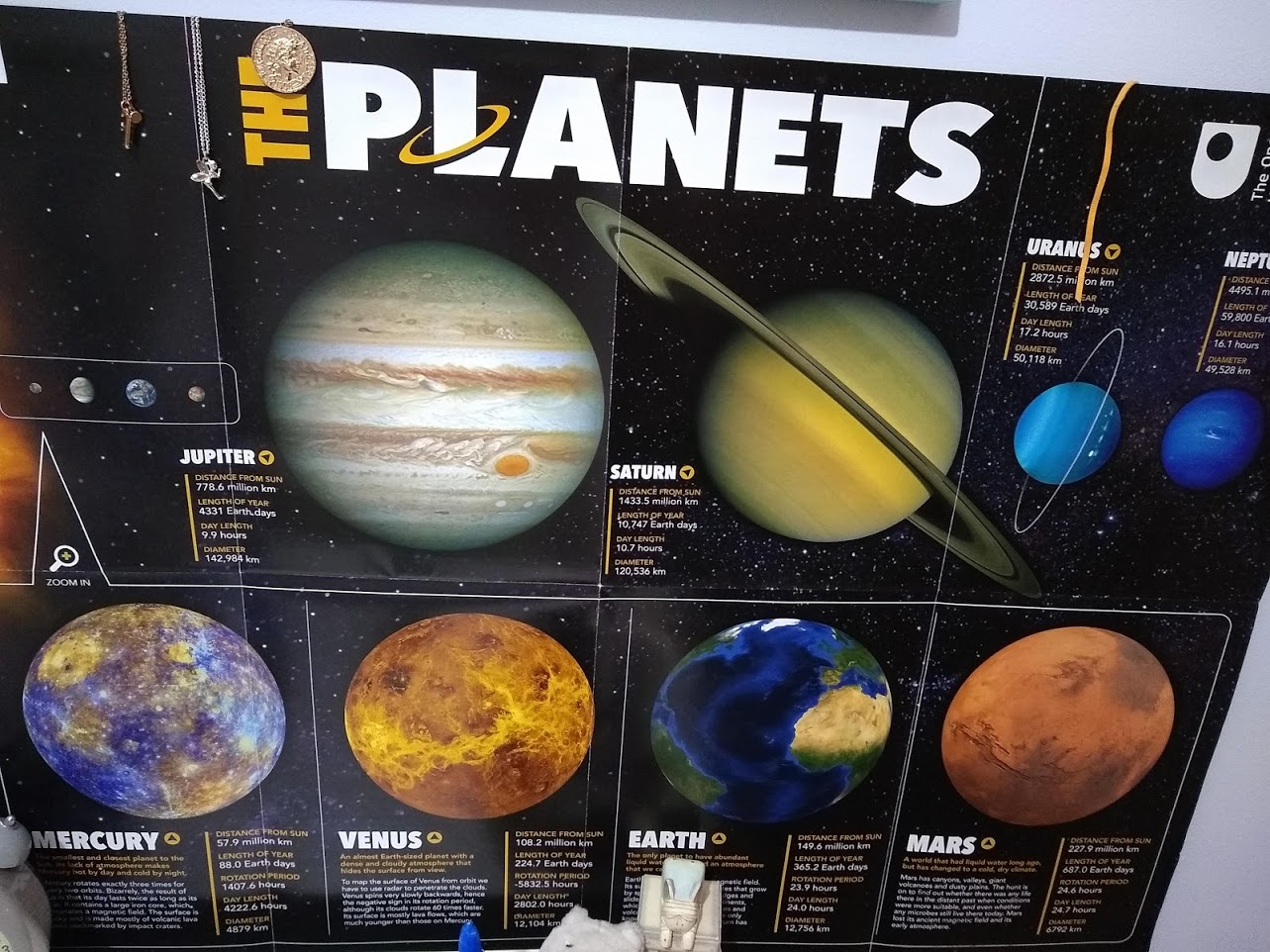
Read moreThe Planets
While scanning a Solar System poster and comparing the planets' distances from the sun I noticed a pattern I'd not seen before. I've been fascinated by space since I was a young child and have been studying astronomy in one form or another all my life but I'd never heard anything like this pattern mentioned.
Skyfall
The last James Bond film I watched was Moonraker, but I recently caught the ending of Skyfall on TV and realised why I don't watch them anymore.
According to wikipedia, the section I saw was when Bond took M to his Skyfall home and with Kincade's help they set up a series of booby traps throughout the house. Silva's men arrived.
Now, these men looked pretty well-trained to me and I'm sure they were fully expecting a booby trapped house. One of the first traps you might expect would be some kind of pressure plate or trip-wire on the entrance to the house grounds.
Yet I watched with disbelief as all Silva's men got out of their jeeps and, when presented with a derelict gateway with waist-high walls either side of it, funnelled through the gate shoulder to shoulder.
Read moreThe Sinclair ZX Spectrum Keyboard
When I was 12 years old, I got sight of an actual computer. One day at my cousins' house, set on a table and wired up to their TV was a small, black rectangle. They were pressing keys on it to play games (Schizoids and Ant Attack I remember). I was curious - the games looked more interesting than the simple arcade games I played on my Atari console. I got closer and peered over and saw the keyboard and it changed my life. Here's what I saw:
